Comprehensive Caller Insight on 8884267826 and Risk Factors

The analysis of 8884267826 focuses on caller identity signals, timing patterns, and routing metadata to identify unverified origins. It weighs motive indicators such as inquiry type and engagement cadence against objective metrics to reduce ambiguity. Risk signals include duration anomalies and rapid contact sequences that challenge verification standards. The findings offer data-driven verification and standardized response protocols, but the implications remain contingent on context and interpretation, inviting further assessment to determine appropriate protective actions.
What 8884267826 Reveals About Caller Identity
The number 8884267826 serves as a data point for assessing caller identity signals, with analysis focusing on patterns in access location, call timing, and related metadata.
The evaluation identifies an unverified caller tendency, increasing detected identity risk through irregular time stamps and atypical routing.
Findings emphasize objective metrics, reducing ambiguity while enabling controlled freedom in risk assessment and response strategies.
Decoding Motives: Why This Number Callers Might Dial In
Examined through a data-driven lens, the motives behind calls from 8884267826 can be inferred by correlating timing patterns, caller routing, and engagement metrics; preliminary analysis suggests a mix of informational inquiries, service solicitations, and potential automated outreach.
Decoding motives reveals patterns tied to caller identity risk signals, protective practices, and strategic engagement, guiding scrutiny without assuming intent.
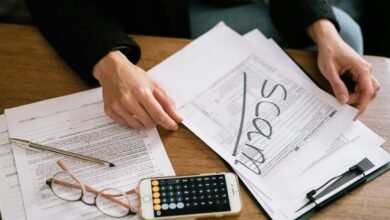
Red Flags and Risk Signals for Businesses From 8884267826
Red flags and risk signals associated with 8884267826 emerge from observable call characteristics and engagement patterns rather than subjective impressions. This analysis identifies measurable indicators: call duration anomalies, repeated contact across short intervals, inconsistent caller identity, and motive divergence between stated purpose and behavior.
Red flags and risk signals align with objective data, guiding prudent, freedom-respecting business decisions.
Practical Verification and Protective Practices for Safe Interaction
Practical verification and protective practices for safe interaction emphasize objective verification steps, consistent with data-driven risk assessment. The analysis highlights caller verification protocols, corroborating data sources, and standardized identity protection measures. Red flags and scam indicators are cataloged to inform rapid decision-making, enabling disciplined interaction. An evidence-based framework supports freedom to engage while minimizing exposure to exploitative patterns and fraudulent attempts.
Conclusion
In the data’s quiet hum, 8884267826 emerges as a measured signal with patterns that speak in cadence. Timings, routes, and engagement metrics form a lattice, revealing motives as probabilistic shadows rather than certainties. The analysis identifies risk as irregular timing, rapid retries, and inconsistent identity signals, guiding guarded responses. Practically, standardized verification and protective protocols translate this empirical insight into actionable safeguards, transforming ambiguous contact into a calibrated risk spectrum and a disciplined contact-management routine.