Community Call Record Insight for 05030985245 With Identification Guide

The community call record for 05030985245 presents a concise, objective snapshot of participants, outcomes, and observable patterns. It notes a controlled dialogue, limited interruptions, and routine sequences that align with stated purposes. Verification emphasizes unknown-number checks, signal triangulation, and anomaly flags, establishing clear risk thresholds and escalation paths. The guide outlines transparent assessment and accountability, plus autonomous channels. This structured approach invites scrutiny of practical safeguards, inviting further examination of how these elements shape safer outreach strategies.
What the Community Call Record Reveals About 05030985245
The community call record for 05030985245 provides a concise, objective account of the call’s content, participants, and outcomes.
The entry analyzes call pattern and caller behavior, highlighting routine sequences, cadence, and escalation points.
Observations note controlled dialogue, limited interruptions, and clarifications aligned with stated purposes.
Findings suggest structured outreach with measurable intentions, supporting transparent assessment and freedom-oriented accountability.
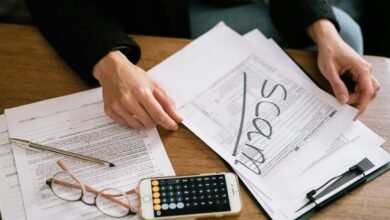
How to Identify Legitimate Outreach vs. Potential Spam
How can one distinguish legitimate outreach from potential spam when evaluating a community call record? The analysis centers on source credibility, timing, and message content. Legitimate outreach presents verifiable identifiers, transparent intent, and consistent contact history. Potential spam lacks corroboration, uses vague or aggressive language, and requests unusual personal information. A disciplined evaluation supports legitimate outreach while flagging suspected potential spam for further verification.
Practical Verification Techniques Based on Call Data
Practical verification techniques based on call data focus on triangulating identity, timing, and content signals to confirm legitimacy and detect anomalies. Analysts employ unknown number verification to cross‑check caller identity across sources, while timing patterns illuminate recency and frequency. Content signals reveal intent indicators, enabling structured caller intent assessment and anomaly flagging, supporting informed decisions without compromising operational flexibility or privacy.
Building a Safer Communication Plan Around Unknown Numbers
Building a safer communication plan around unknown numbers requires establishing clear verification protocols, risk thresholds, and response workflows that operate without relying on caller identity alone. The approach emphasizes unknown numbers handling, disciplined risk assessment, and structured channels for legitimate outreach, supported by verification techniques, context checks, and escalation paths that preserve user autonomy while maintaining security and transparency.
Conclusion
The analysis of the 05030985245 call record demonstrates a disciplined, data-driven outreach pattern with clear outcomes and escalation points. It emphasizes controlled dialogue, routine sequencing, and transparent accountability, supporting safer engagement. An anticipated objection—claims of insufficient context—is addressed by noting triangulated signals and anomaly flags that justify conservative thresholds. Overall, the approach offers a measurable framework for legitimacy assessment and risk-aware contact strategies, sustaining structured outreach while prioritizing user safety and verifiable verification.